Cyberware Defense Global
The Challenge
In the midst of a high-octane hackathon, our mission was clear: build a cutting-edge cybersecurity website that not only showcased our firm’s robust capabilities but also demonstrated our innovative approach under extreme time pressure. We had to distill complex security strategies into a narrative that resonated with clients, reassuring them that their digital assets were shielded by the best in the business.
Problem Statement
Clients needed a platform that clearly communicated the range of services offered, highlighting the unique value propositions and innovative solutions tailored to their needs. The challenge was to create a seamless, engaging experience that effectively showcased the client's expertise and offerings.
🔍 Researching
With the hackathon clock ticking, we dove straight into rapid research. We skimmed through the latest industry reports, real-time threat intelligence, and competitive analyses to understand the evolving tactics of cybercriminals. Every minute was spent gathering insights that highlighted the vulnerabilities businesses face, ensuring our website would speak directly to the critical concerns of potential clients.
This swift yet thorough exploration laid the groundwork for a strategy that was both timely and robust, ensuring that our solution was informed by the very latest in cybersecurity trends.
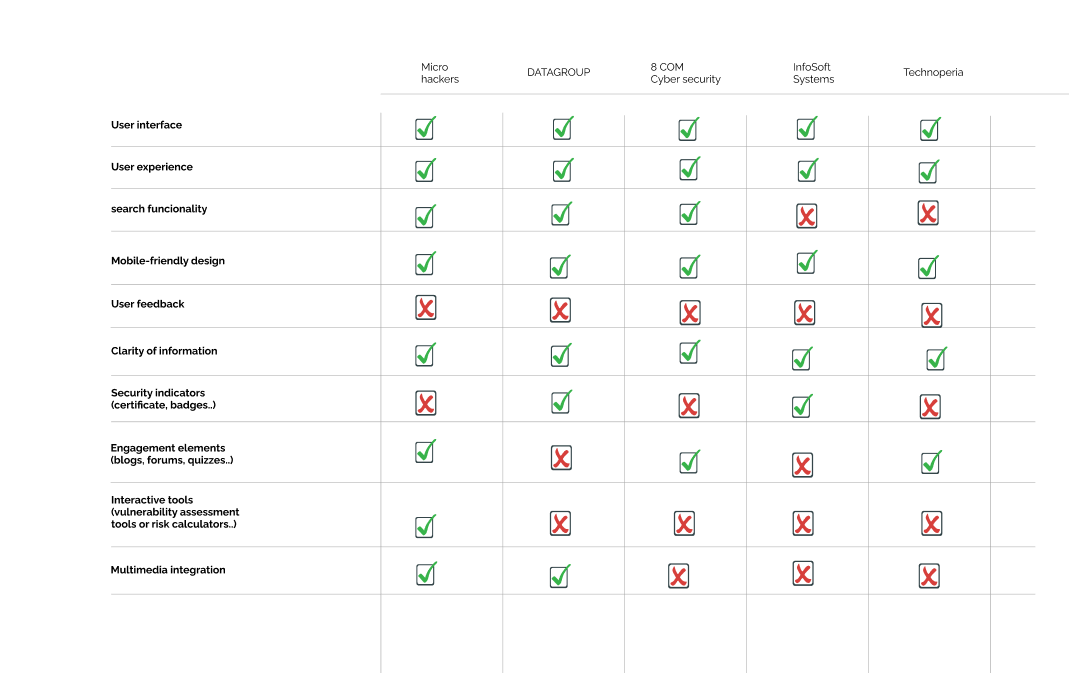
👥 Creating Your Average User’s Needs
User Persona
Key Needs:
Under the pressure of a hackathon, we quickly distilled our findings into clear user needs. Our audience—ranging from agile startups to established enterprises—required swift reassurance that their sensitive data was secure. We envisioned a digital experience where every interaction, from concise service overviews to detailed client testimonials, provided the clarity and confidence they sought in a cybersecurity partner. This clear definition of user requirements ensured that every design decision was laser-focused on delivering exactly what our clients needed most in times of cyber crisis.Armed with research, we mapped out the core needs of our future users. Gen Z demanded a platform that was visually engaging, intuitive, and packed with bite-sized learning modules. The traditional heavy-handed approach to financial education was out; what was in was an experience that felt like a game, complete with rewards and community challenges. Every design decision was driven by the goal to make finance feel accessible and even fun.
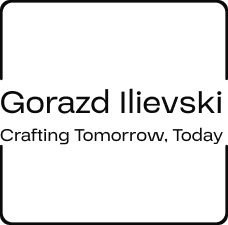
📊 Analyzing
Our analysis phase was both rapid and rigorous. We pinpointed the major pitfalls in traditional cybersecurity communication, such as overwhelming jargon and static content, and recognized the need for simplicity and transparency. This quick yet thorough analysis became the cornerstone of our design, ensuring that our website would break down complex security protocols into easily digestible insights. Our team scrutinized each competitor’s offering to uncover hidden opportunities for simplification, setting the stage for a more intuitive and approachable platform. Our moodboard reflected all of these thoughts and prepared us quite fittingly for the journey ahead.
🗺️ Mapping Your Product
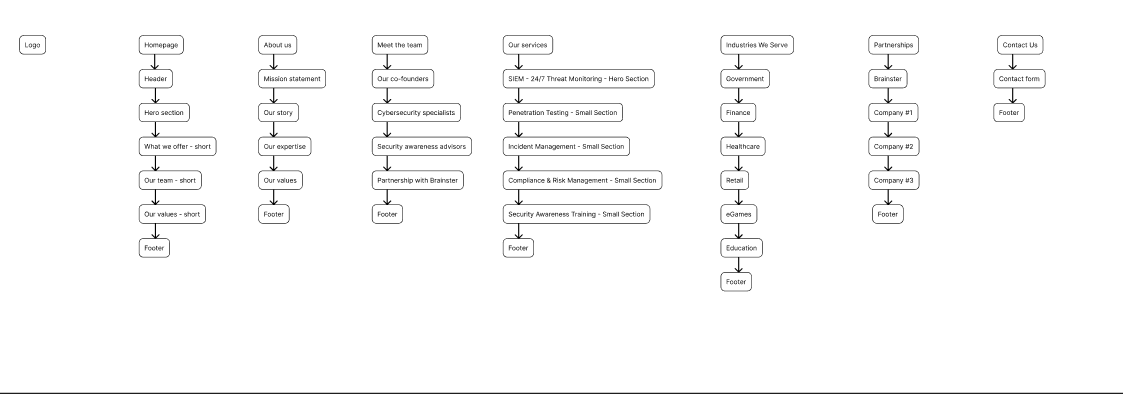
In a series of quick sprints, we mapped out the user journey for our website. Despite the hackathon’s intense pace, we developed a strategic blueprint that guided visitors from an engaging landing page to detailed service descriptions and interactive security visualizations. Every step was designed to build trust and clearly communicate our proactive defense strategies, turning each page into a seamless part of the client’s journey toward security. This product map became our strategic playbook, aligning every component of the website with the ultimate goal of delivering a secure and confident user experience.
📐 Framing Your Wires
The creative energy of the hackathon propelled us into rapid wireframing. Our ideas swiftly took shape as digital sketches, where we experimented with intuitive navigation and dynamic layouts. These wireframes served as our testing ground—an essential phase where we balanced technical depth with user-friendly design, ensuring that every screen clearly conveyed our cybersecurity prowess. Each iteration of the wireframes brought us closer to a layout that seamlessly integrated function and form, turning abstract concepts into tangible blueprints for success.
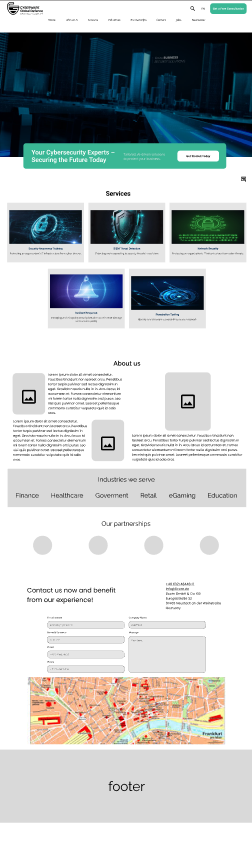




Every iteration was a leap toward perfection, each wireframe a step closer to a user experience that felt natural, engaging, and unmistakably modern.
🎨 Designing Your Product
Design System Highlights:
- Color palette: #FF7955 (primary), #335271 (secondary), #FFFFFF (tertiary), #000000 (text)
- Typography: Montserrat and Open Sans
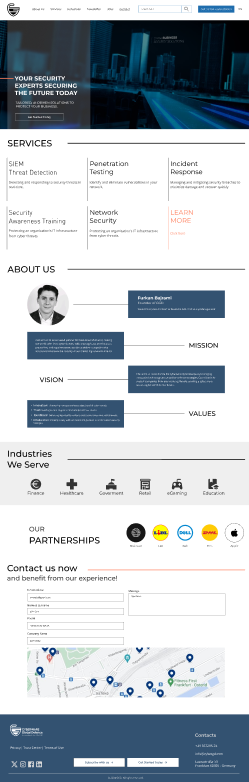


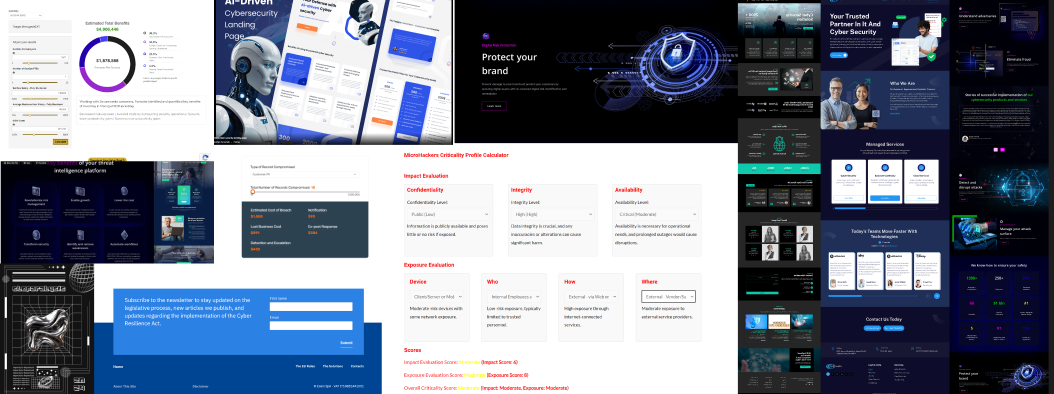
🛠️ Prototyping
Transitioning from design to a working model, we rapidly built an interactive prototype under hackathon constraints. This functional version allowed us to simulate the user journey, test interactive elements, and gather immediate feedback. The prototype was our proving ground, confirming that our innovative narrative and streamlined user experience could thrive even under the pressure of a rapidly evolving digital battlefield. Every bug we encountered and every user insight we gathered during prototyping only fueled our drive to refine the experience, making our solution even more resilient and effective.
Tools Used:
- Figma
🎉 DING! All Done
As the hackathon drew to a close, our cybersecurity website emerged as a testament to rapid innovation and teamwork. Every element—from the intuitive user journey to the dynamic visual storytelling—demonstrated our firm’s capability to protect clients in an increasingly hostile digital world. Even though the project was born under the relentless pressure of a timed competition, it highlighted our unwavering commitment to transparency, technical excellence, and creative problem-solving. While the hackathon was a temporary crucible of challenge, the insights and innovations born from it continue to shape our approach to cybersecurity, proving that even under the highest pressure, ingenuity thrives.